C# Obfuscator Master
C# Obfuscator Master can encrypt and obfuscate DLL and EXE files written in C# (including WinForms, WPF, Unity games, console apps, and more). It supports .NET Framework 2.0 ~ .NET Framework 4.x and .NET Core 2.0 - .NET 8. In addition to code encryption and obfuscation, C# Obfuscator Master can also pack EXE programs, add tamper protection, inject junk data, and more — effectively protecting the intellectual property of C#-written programs, preventing code logic from being copied, and guarding against program tampering.
Why Do You Need Code Obfuscation?
C# is a managed language. The IL intermediate code it generates can be easily decompiled by reverse engineering tools. Statistics show that over 83% of commercial software has faced code reverse-engineering risks, leading to core algorithm leaks and license bypasses. C# Obfuscator Master provides:
- Control flow obfuscation to scramble execution logic
- String encryption to hide sensitive information
- Metadata obfuscation to rename key elements
- Dynamic anti-debug mechanisms
- Code virtualization protection
Comparison with Other Tools
In the code protection space, popular open-source solutions like ConfuserEx were once widely used, but their last update was in 2016 — unable to support .NET Core and other modern frameworks, and easily defeated by modern decompilers like dnSpy. Worse, the open-source community lacks ongoing maintenance, leaving developers without help when compatibility issues arise. Commercial tools like Eazfuscator offer basic protection, but their annual subscription fees of over $2,000 are prohibitive for small developers, and their fixed encryption patterns can be cracked with publicly available de-obfuscation scripts (e.g., de4dot plugins). Some legacy tools haven't been updated in so long that they can't even recognize C# 9.0 syntax features, causing programs to crash after obfuscation.
C# Obfuscator Master breaks through these industry pain points: It uses a dynamic encryption engine that generates random instruction sets and mutation algorithms on every obfuscation run — even the same code processed multiple times produces completely different protection layers, eliminating pattern-based attacks. The development team maintains a rapid update cadence, continuously countering the latest techniques in ILSpy, dnSpy, and other decompilers. The proprietary "Fragmented Virtual Execution" technology breaks critical code into encrypted fragments that are only dynamically reassembled in memory at runtime, rendering static decompilation ineffective. Affordable licensing includes continuous upgrade services and a technical support group that responds to issues within 10 minutes — true enterprise-grade protection at indie developer pricing.
Features
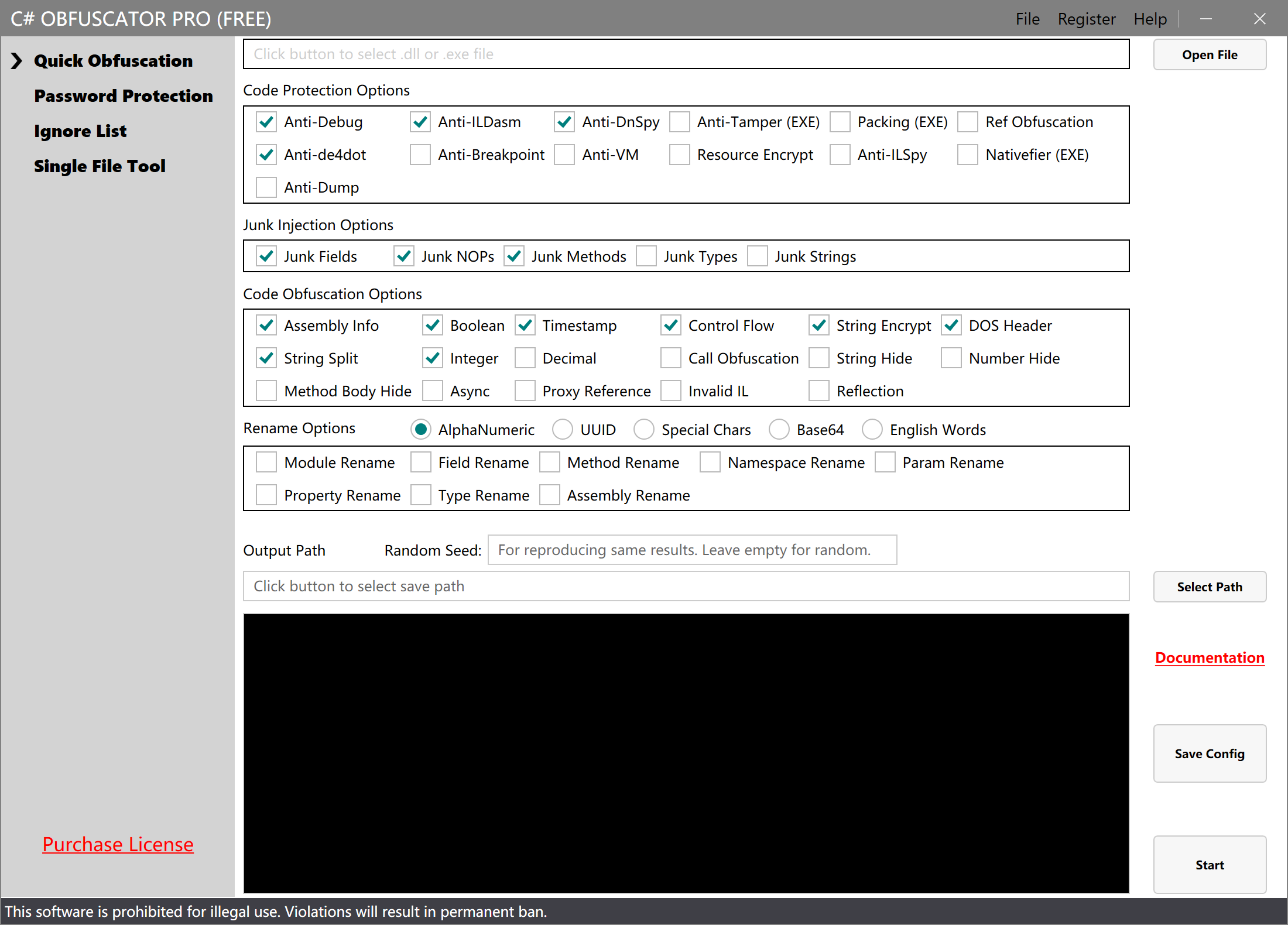
- Supports WinForms/WPF/Unity across all frameworks
- 20+ obfuscation options freely combinable
- Smart compatibility with .NET 2.0–8.0
- Triple encryption architecture
- 30-second rapid processing workflow
Core Technical Advantages
1. Full Framework Compatibility
- Cross-platform support: Fully supports WinForms desktop apps, WPF enterprise applications, Unity3D games (2018–2022 full range), console tools, and more
- Special scenario optimization: Deep compatibility with Unity IL2CPP mode, resolving crashes caused by traditional tools
- Server-side support: Compatible with ASP.NET Core WebAPI/Blazor and other server-side program encryption
2. Full Version Coverage
- Legacy version compatibility: Full support for .NET Framework 2.0/3.5/4.0/4.5/4.8 and older frameworks
- Latest technology support: Native compatibility with .NET Core 2.1–8.0 and .NET 5/6/7/8, auto-detects SDK features
- Mixed development support: Handles C# code protection for Xamarin/MAUI and other cross-platform solutions
3. Control Flow Obfuscation
- Multi-level instruction decomposition: Splits continuous logic into random sub-blocks, scrambling original execution order
- Fake branch injection: Inserts dead code traps to confuse static analysis tools
- Opaque predicates: Uses mathematically hard problems to construct conditionals, making post-decompile execution paths undeterminable
4. Enterprise-Grade Protection System
- Dynamic packing: Each encryption uses random algorithms, preventing signature-based detection
- Triple tamper protection: File hash verification + memory integrity check + runtime environment validation
- Decompiler traps: Injects crash code targeting ILSpy/dnSpy
5. Intelligent Noise System
Junk Injection Engine:
- Randomly generates invalid classes/methods/properties (configurable count)
- Injects noise strings (Base64/UUID/random characters)
- Creates fake control flow branches
6. Flexible Renaming Strategy
12 Naming Modes:
- Alphanumeric mix (Class_01a)
- UUID style (CA7356F8-3E3D)
- Special symbols (_$V1@Func)
- Natural language obfuscation (Apple_Tree)
Multi-level control:
- Namespace renaming
- Class/struct obfuscation
- Method/field transformation
7. Native Code Protection
- IL to Native: Critical code converted to x86 instructions
- Virtualized execution: Sensitive logic runs inside a virtual machine
- Anti-dump mechanism: Prevents memory image extraction
8. Fine-Grained Configuration
Smart Ignore List:
- Three-level whitelist: method / class / assembly
- Automatically skips methods called via reflection
Want to Learn More or Try It for Free?
Contact
If you need sales consultation or encounter any issues during software usage, you can reach us by email:
📧 Email
Email Address: leapever@foxmail.com